Diploma in Cyber Security & Ethical Hacking
Guaranteed Job Opportunities | Salary: ₹ 6 LPA to 18 LPA | 3 Capstone Projects
Eligibility: Any Final-Year Student or Graduate Pass-out or Aspiring Working Professionals
Why Learning Ethical Hacking Will Secure Your Future!
According to reports, the global cybersecurity market is expected to grow at a CAGR of 11.0% from 2022 to 2030, reaching a market size of USD 403.4 billion by 2030. This growth is driven by increasing cyber threats, data breaches, and the need for robust security measures across industries.
Eligibility:
- Any Final Year Student or Graduate Pass-out with basic computer knowledge can apply; a background in Computer Science or IT is beneficial but not required.
- Working professionals aspiring to do career into Cyber Security field.
About This Program
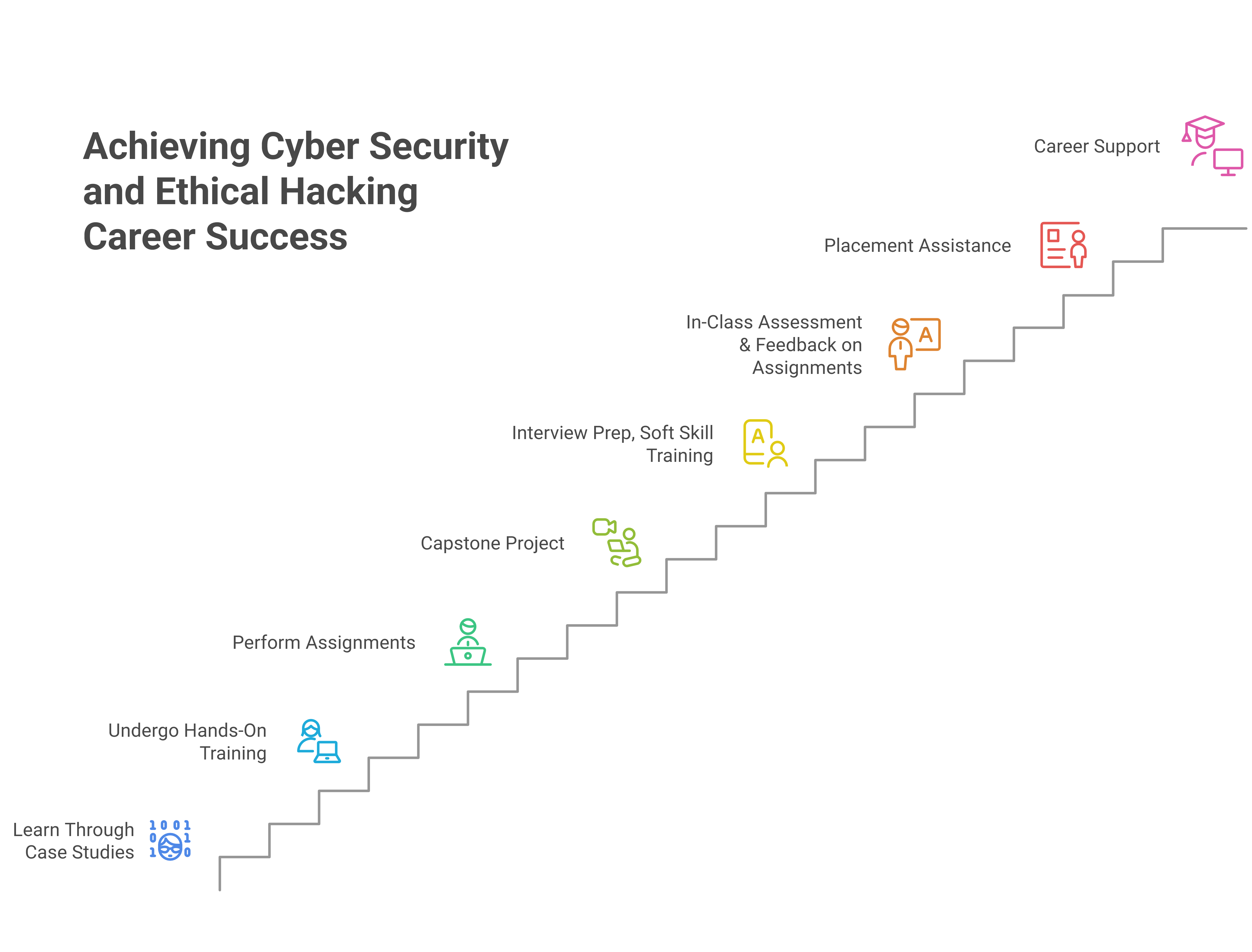
After extensive research and consultations with industry experts, we have designed a Diploma in Cyber Security & Ethical Hacking (DCSEH) program, tailored for job seekers and professionals aiming to build a career in the rapidly growing cybersecurity field. This comprehensive program blends live lectures with online sessions to equip you with essential skills in ethical hacking, network security, penetration testing, cyber risk management, and more. Through hands-on training, you will gain a deep understanding of various attack vectors, countermeasures, and industry-standard tools used to protect organizations from cyber threats. The program also incorporates a capstone project, giving you practical exposure to real-world security challenges and solutions.
Additionally, we focus on soft skills development through our Employability Development Program, ensuring you are well-prepared for the job market. Our Diploma in Cyber Security & Ethical Hacking (DCSEH) is a unique program that includes expert-led sessions on ethical hacking techniques, network security protocols, and cyber defense mechanisms. With 100% placement support and rigorous placement drives within our 500+ client base, we aim to open doors to multiple job opportunities in this high-demand field. Cybersecurity is one of the fastest-growing industries globally, with the demand for skilled professionals continuing to surge.
Various sectors have ramped up their cybersecurity efforts, creating more job opportunities for professionals in this domain, including:
- BFSI (Banking, Financial Services, and Insurance)
- Telecommunication
- IT & ITES (Information Technology and IT-Enabled Services)
- Government & Public Sector
- Retail & E-commerce
- Healthcare & Life Sciences
- Energy & Utilities
- Media & Entertainment
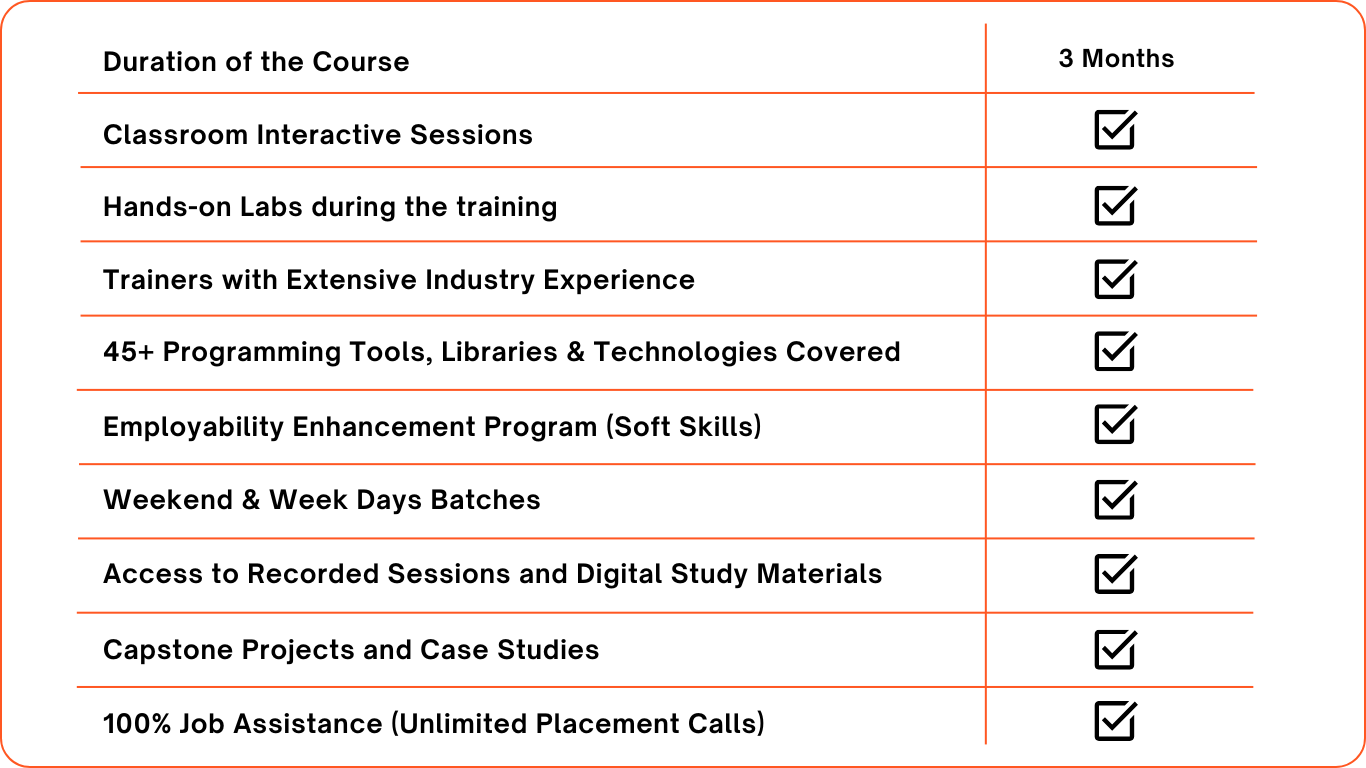
Highlights:
- SOC Analyst – Level 1 (Security Operations Center Analyst)
- Cyber Security Analyst – Junior
- Information Security Analyst – Associate
- Real-World Simulation Labs
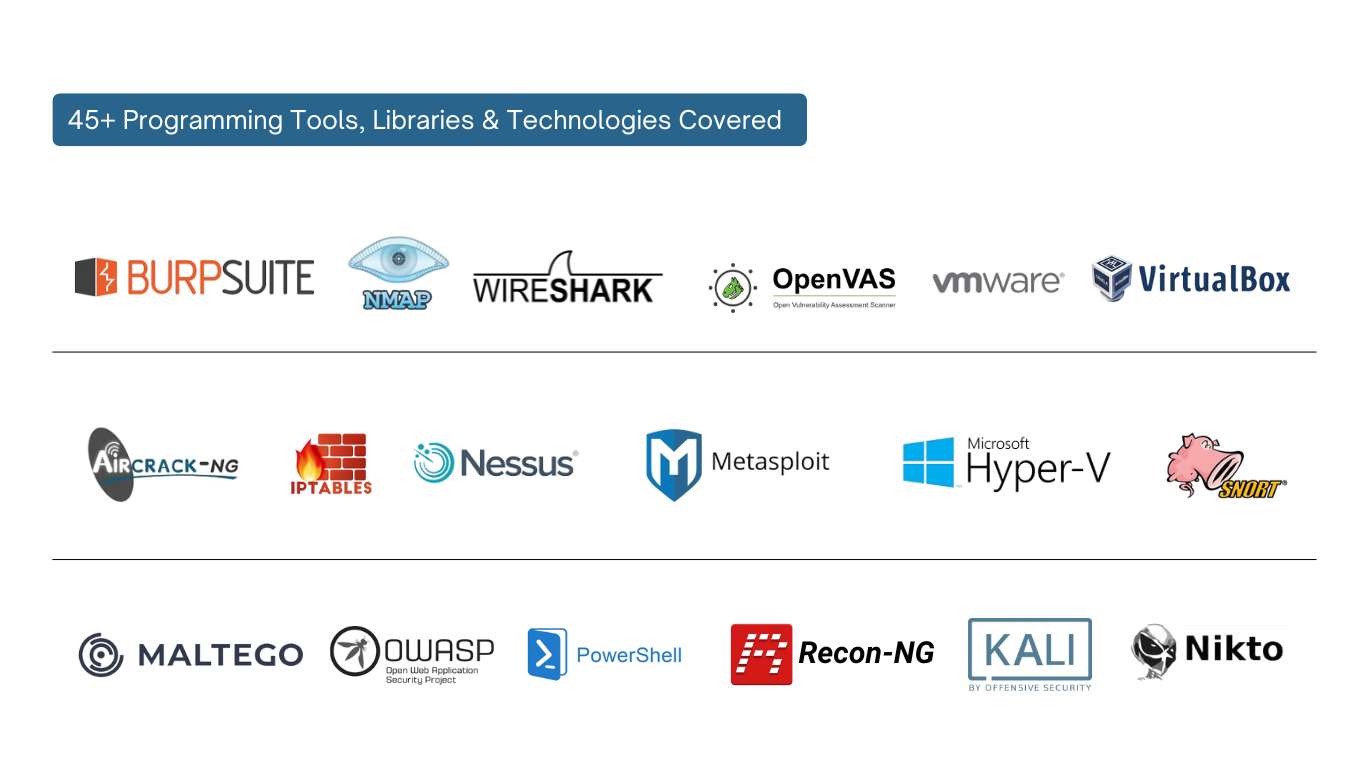
- 45+ Programming Tools, Libraries & Technologies Covered
- Employability Enhancement Program (Soft Skills)
- Duration of 3 Months: Weekdays & Weekend Batches
- Industry Exposure : Capstone Projects
- Starting Salary Range: 2.5 LPA to 3.5 LPA
- 100% Job Assistance (Unlimited Placement Calls)
Learning Path:
Tools and Technologies:
Course Content:
Introduction to Networking
- What is networking?
- How the Internet Operates
- Types of Networks (LAN, WAN, VLAN, etc.) OSI Model & TCP/IP Stack
- IP Addressing (IPv4/IPv6), Subnetting, and CIDR
Network Devices and Protocols
- Switches, Routers, Firewalls
- Common Protocols: HTTP, HTTPS, DNS, DHCP, FTP, SMTP VPN, NAT, ARP, IPSEC
- Packet Analysis Basics (Wireshark, tcpdump)
Network Troubleshooting and Tools
- Firewall, IDS/IPS Overview
- VLAN, VPN, NAT
- Ping, Traceroute, ARP, and NSLookup
- Common Network Vulnerabilities
Windows Administration Basics
- Windows Architecture / File System/ File Permissions
- Practical: SAM Files & System Files
- Password Hashing (LM, NTLM, Kerberos)
- Filesystem and Registry Structure
- User and Group Management
Windows Networking and Security
- Active Directory
- Lightweight Directory Access Protocol (LDAP)
- Task Scheduling
- Windows Event Logs
- Windows Networking Features (SMB, RDP, PowerShell Remoting)
Linux Fundamentals & Lab Setup
- Introduction to Linux
- Linux Architecture and Distributions
- Installing VirtualBox & Kali
- Shell and File System Basics
- User and Group Management
- File Permissions and Ownership (chmod)
- Linux Command (ifconfig, ip, netstat, etc.)
- Monitoring and Logs (top, ps, dmesg, syslog)
Introduction to Information Security and Ethical Hacking
- Types of Hackers
- CIA Triad
- Key Concepts and Terminologies (CVE, CVSS, TTPs)
- Cyber Kill Chain Methodology
- MITRE ATT&CK Framework
- Risk Management
- Verticals of security team in Industry
- Information Security Laws and Standards
- Cyber Law in different Countries
Footprinting and Reconnaissance
- What is Digital Footprinting
- Types of Information Gathered (Active/Passive)
- Social Engineering, Email Footprinting, and Website Footprinting (Dorking, Maltego, Spiderfoot, Shodan)
- Countermeasure
- Anonymization Tools
Network Exploration
- Overview of Network Scanning
- Types of Scans: TCP, SYN, ACK, and UDP Packet Crafting (Hping3, Scapy)
- Scanning (NMAP, Netcat, IKE Scan)
- Enumeration Techniques & Introduction to Metasploit
- NetBIOS Enumeration
- Enumerating SNMP using SnmpWalk and Nmap
- DOS Attacks (Syn flood, smurf attack, Ping of death)
Vulnerability Management
- Vulnerability Assessment Techniques
- Automated vs. Manual Assessment
- Types of Vulnerabilities: Network, System, and Application
- Tools for Vulnerability Analysis
- Nessus, OpenVAS, and Qualys (Practical)
- Interpreting Vulnerability Reports
- Prioritizing Vulnerabilities
- Remediation Strategies
Password Hacking
- Types & Techniques of Password Cracking
- Cracking Passwords (Bruteforce, SSH)
- Privilege Escalation & How to Defend Against Privilege Escalation
- Maintaining Access (RCE, Persistence) & Covering Tracks
Network Sniffing
- Network Sniffing Techniques
- Protocols Susceptible to Sniffing
- MAC Spoofing, ARP Poisoning
- DHCP & Starvation Attacks
- Countermeasures
Malware Analysis
- Types of Malware (Trojan, Fileless, Worms)
- Malware Analysis (Static/Dynamic) with tools
Wireless Network Hacking
- IEEE 802.11, Type of wireless networks
- Wireless Encryption Techniques
- Wireless Discovery with Tools
- Cracking WPA/WPA2
- MITM, Deauth Attack
- Evil Twin Attack
Web App Security
- Basics of how websites work – Client-Server model, HTTP request/respons
- HTTP headers – request, response, and security headers
- Introduction to Burp Suite – setup, intercept, repeater, intruder
- Web servers – Apache, IIS, Nginx basics & common misconfigurations
- OWASP Top 10 overview
- Evasion techniques – IDS/IPS bypass, honeypots detection
- Same Origin Policy & CORS exploitation
- Same Origin Policy & CORS exploitation
- Session hijacking & JWT token attacks
- Password brute-forcing techniques
- XSS (Reflected, Stored, DOM) & HTML injection
- OTP bypass attacks
- CSRF vs SSRF exploitation
- Parameter tampering & privilege escalation
- Clickjacking attacks
- File upload vulnerabilities & remote code execution
- SQL injection – classic, blind, time-based, error-based
- Buffer overflow in web context
- Countermeasures & secure coding practices for all vulnerabilities
Web servers – Apache, IIS, Nginx basics & common misconfigurations
- OWASP Top 10 overview
- Evasion techniques – IDS/IPS bypass, honeypots detection
- Same Origin Policy & CORS exploitation
- Session hijacking & JWT token attacks
- Password brute-forcing techniques
- XSS (Reflected, Stored, DOM) & HTML injection
- OTP bypass attacks
- CSRF vs SSRF exploitation
- Clickjacking attacks
- Parameter tampering & privilege escalation
- File upload vulnerabilities & remote code execution
- SQL injection – classic, blind, time-based, error-based
- Buffer overflow in web context
- Countermeasures & secure coding practices for all vulnerabilities
Introduction To Mobile Architecture
- OWASP Top 10
- Introduction to IOS & Android Architecture
- Rooting Android (ABD)
Mobile Application Pentesting
- Andro Rat
- Android Pentesting & Tools
- MDM & Mobile Security Guidelines
Cloud Security
- Cloud Computing Concepts
- Types of Cloud Services (IaaS, PaaS, SaaS)
- Cloud Deployment Models (Public, Private, Hybrid) (Practical)
- Cloud Security Challenges
- Data Breaches, Account Hijacking, and Insider Threats
- Cloud Security Tools
- CASBs, Cloud Encryption, and IAM Solutions
Incident Response and Handling
- Incident Response Methodology
- Preparation, Identification, Containment, Eradication, Recovery, and Lessons Learned
- Steps in Incident Handling
- Detection, Analysis, and Documentation Tools for Incident Response
- SIEMs, Forensic Tools, and Threat Intelligence Platforms (Practical)
Cryptography
- Cryptography Concepts and Encryption Algorithms
- Countermeasures
Interview Preparation
- Preparing for an Interview
- Interview Question Discussion
Analysing and Solving Vulnerable Machines: 1
- Reconnaissance (Information Gathering)
- Vulnerability Scanning
- Exploitation
- Privilege Escalation
- Post-Exploitation
Analysing and Solving Vulnerable Machines: 2
- Documentation
- Analysis
- Mitigation
- Reporting
- Cleanup and Restoration
Job Roles:
By completing this course, you will be equipped to take on roles such as:
- SOC Analyst – Level 1 (Security Operations Center Analyst)
- Cyber Security Analyst
- Information Security Analyst – Associate
- Threat Monitoring Analyst – Trainee
- Incident Response Analyst – Associate
- Associate Penetration Tester
- Junior Ethical Hacker
- Vulnerability Assessment Analyst – Trainee
- Application Security Analyst – Junior
- Red Team Associate
- Information Security Associate – GRC
- Compliance Analyst – Associate
- Risk Analyst – Trainee
- Security Policy Analyst – Junior
- Audit Associate – Information Security
- Forensic Analyst – Associate
- Incident Response Associate
- Cyber Crime Analyst – Trainee
- Network Security Analyst – L1
- Firewall Analyst – Associate
- Endpoint Security Analyst – Junior
- Security Research Associate
- Threat Intelligence Analyst – Junior
- Security Awareness Coordinator – Entry Level
- Bug Bounty Researcher (In-house)
Duration
03 Months
This Course Include
- 45+ Programming Tools, Libraries & Technologies Covered
- Real-World Simulation Labs
- 100% Job Assistance (Unlimited Placement Calls)
- Industry Exposure : 3 Capstone Projects
Enquire Now
Industry Collaboration & Placements
+91-78229 35066 /+91-83297 03277
info@nextgenedu.in






